
0
0
1,203
The transition to 5G infrastructure will likely increase the risk of a new series of Distributed Denial-of-Service (DDoS) attacks. While DDoS attacks range from targeted acts of retaliation, protest, theft, or extortion to pranksters, they all have one objective: disrupt service availability and reduce the ability of a business to function. Service providers building 5G infrastructure must implement a strategy to help mitigate the impact of attacks on bandwidth and subscribers. The move to using more virtualized technology can enable service providers to reduce the force and effectiveness of DDoS attacks more quickly and at scale.
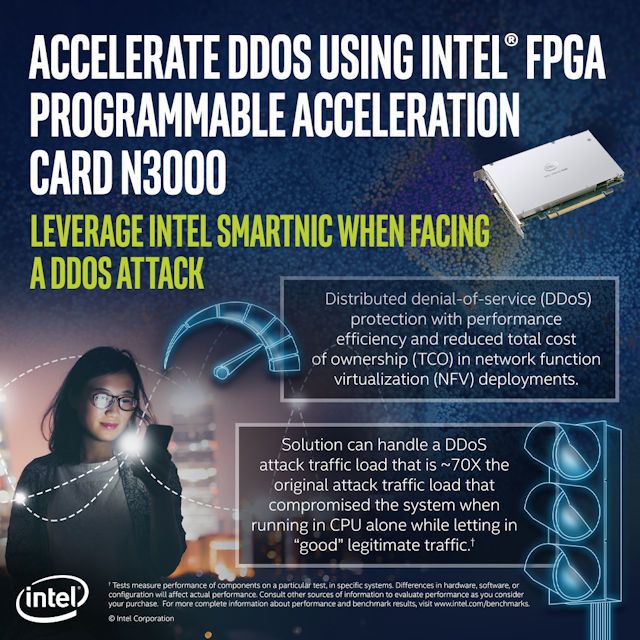
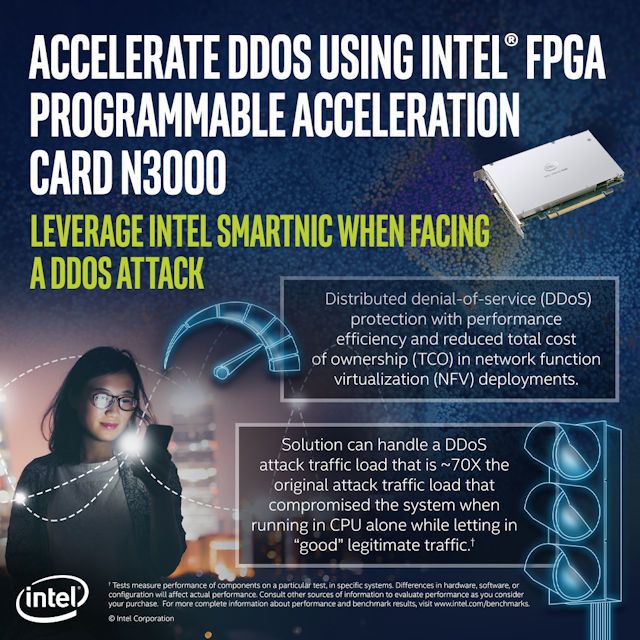
For example, the F5 BIG-IP Advanced Firewall Manager Smart Virtual Edition (AFMVE)—integrated with an Intel® FPGA Programmable Acceleration Card (PAC) N3000—offers such an opportunity. By combining this solution with virtualized 5G infrastructure using commercial off-the-shelf (COTS) servers, service provider networks can automatically detect and better protect themselves faster than current methods against evolving, volumetric DDoS attacks that can negatively affect subscriber and user access to applications and other services.
The Intel FPGA PAC N3000 is dynamically configurable to accelerate multiple workloads such as 5G vRAN, Open vSwitch, Segment Routing v6, Tungsten Fabric, 5G User Plane Function (UPF), vBNG, and security solutions. This allows service providers to deploy a server plus the Intel FPGA PAC N3000 to support many cloud-native network functions or virtual appliances based on services demand at the edge. In testing performed by F5, the BIG-IP AFM Virtual Edition (VE) integrated with an Intel® FPGA PAC N3000, withstood a 70x higher level DDoS attack (TCP RST flood attack) than processing in software in a COTS server. The solution detected and blocked the “bad” attack traffic while letting in “good” traffic.1
In addition to service providers, enterprise organizations undergoing digital transformation will need to respond to these new types of DDoS attacks.
For more information, please see the Solution Brief titled “High Capacity DDoS Protection in Cloud Environments with F5 BIG-IP AFM VE and Intel® FPGA PAC N3000.” (Click on the link to download the solution brief.)
Notices and Disclaimers
1 Based on F5 internal testing using Ixia traffic generators to simulate both “good” traffic and “bad” (TCP RST flood attack) and comparing the results with Intel® FPGA PAC N3000 DDoS protection enabled and running BIG-IP AFM VE firewall in SW only. Test configuration: Dell PowerEdge R740; CPU: Intel® Xeon® Silver 4109T CPU @ 2.00 GHz (8 core/16 threads); KVM version: 1.5.0.; Base OS: CentOS Linux release 7.4.1708 (Core), 1 x Intel® PAC N3000 SmartNIC; Firewall SW: BIG-IP Advanced Firewall Manager Virtual Edition (VE) v15.1.0.4 (Alpha Version). Traffic generation configuration: bad traffic: Ixia IxExplorer IxOS 8.5.1700.5 EA.lnk.; good traffic: Ixia XT80-V2.
Intel® technologies’ features and benefits depend on system configuration and may require enabled hardware, software, or service activation. Performance varies depending on system configuration. No product or component can be absolutely secure. For more complete information about performance and benchmark results, visit www.intel.com/benchmarks.
Software and workloads used in performance tests may have been optimized for performance only on Intel microprocessors. Performance tests, such as SYSmark and MobileMark, are measured using specific computer systems, components, software, operations and functions. Any change to any of those factors may cause the results to vary. You should consult other information and performance tests to assist you in fully evaluating your contemplated purchases, including the performance of that product when combined with other products. For more complete information visit www.intel.com/benchmarks.
Performance results are based on testing as of dates shown in configurations and may not reflect all publicly available security updates. See backup for configuration details. No product or component can be absolutely secure. Results have been estimated or simulated. Your costs and results may vary. Intel technologies may require enabled hardware, software or service activation.
© Intel Corporation. Intel, the Intel logo, and other Intel marks are trademarks of Intel Corporation or its subsidiaries. Other names and brands may be claimed as the property of others.
For example, the F5 BIG-IP Advanced Firewall Manager Smart Virtual Edition (AFMVE)—integrated with an Intel® FPGA Programmable Acceleration Card (PAC) N3000—offers such an opportunity. By combining this solution with virtualized 5G infrastructure using commercial off-the-shelf (COTS) servers, service provider networks can automatically detect and better protect themselves faster than current methods against evolving, volumetric DDoS attacks that can negatively affect subscriber and user access to applications and other services.
The Intel FPGA PAC N3000 is dynamically configurable to accelerate multiple workloads such as 5G vRAN, Open vSwitch, Segment Routing v6, Tungsten Fabric, 5G User Plane Function (UPF), vBNG, and security solutions. This allows service providers to deploy a server plus the Intel FPGA PAC N3000 to support many cloud-native network functions or virtual appliances based on services demand at the edge. In testing performed by F5, the BIG-IP AFM Virtual Edition (VE) integrated with an Intel® FPGA PAC N3000, withstood a 70x higher level DDoS attack (TCP RST flood attack) than processing in software in a COTS server. The solution detected and blocked the “bad” attack traffic while letting in “good” traffic.1
In addition to service providers, enterprise organizations undergoing digital transformation will need to respond to these new types of DDoS attacks.
For more information, please see the Solution Brief titled “High Capacity DDoS Protection in Cloud Environments with F5 BIG-IP AFM VE and Intel® FPGA PAC N3000.” (Click on the link to download the solution brief.)
Notices and Disclaimers
1 Based on F5 internal testing using Ixia traffic generators to simulate both “good” traffic and “bad” (TCP RST flood attack) and comparing the results with Intel® FPGA PAC N3000 DDoS protection enabled and running BIG-IP AFM VE firewall in SW only. Test configuration: Dell PowerEdge R740; CPU: Intel® Xeon® Silver 4109T CPU @ 2.00 GHz (8 core/16 threads); KVM version: 1.5.0.; Base OS: CentOS Linux release 7.4.1708 (Core), 1 x Intel® PAC N3000 SmartNIC; Firewall SW: BIG-IP Advanced Firewall Manager Virtual Edition (VE) v15.1.0.4 (Alpha Version). Traffic generation configuration: bad traffic: Ixia IxExplorer IxOS 8.5.1700.5 EA.lnk.; good traffic: Ixia XT80-V2.
Intel® technologies’ features and benefits depend on system configuration and may require enabled hardware, software, or service activation. Performance varies depending on system configuration. No product or component can be absolutely secure. For more complete information about performance and benchmark results, visit www.intel.com/benchmarks.
Software and workloads used in performance tests may have been optimized for performance only on Intel microprocessors. Performance tests, such as SYSmark and MobileMark, are measured using specific computer systems, components, software, operations and functions. Any change to any of those factors may cause the results to vary. You should consult other information and performance tests to assist you in fully evaluating your contemplated purchases, including the performance of that product when combined with other products. For more complete information visit www.intel.com/benchmarks.
Performance results are based on testing as of dates shown in configurations and may not reflect all publicly available security updates. See backup for configuration details. No product or component can be absolutely secure. Results have been estimated or simulated. Your costs and results may vary. Intel technologies may require enabled hardware, software or service activation.
© Intel Corporation. Intel, the Intel logo, and other Intel marks are trademarks of Intel Corporation or its subsidiaries. Other names and brands may be claimed as the property of others.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.