Authors: Anil Rao, VP & GM of Systems Architecture Engineering in the Office of the CTO, Liz Porter, President of Leidos Health Group & Doug Barton, Chief Technology Officer of Leidos Health Group
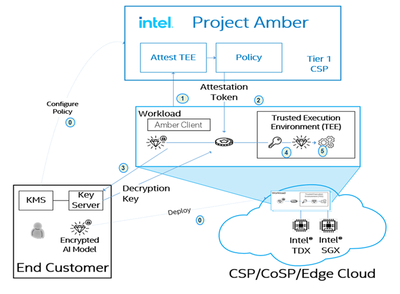
Trust is the core of security, and attestation — proving the identity and integrity of software and hardware to a remote server — is the core of trust. Intel’s new verification service, codenamed Project Amber, uncouples this critical assurance process from cloud providers, instead delivering independent, agnostic and portable attestation as a service-based implementation. It’s a truly disruptive innovation in security technology, with many potential benefits for customers, partners, and developers.
Project Amber enables organizations to more securely scale and move workloads across a wider range of edge, on-premise, and cloud environments — all with better protection for in-use data and intellectual property. Verification of trustworthiness by an independent authority provides a solid security foundation for confidential computing and enables new usages in AI, multi-party compute and federated learning. Integrating with a “third party” like Project Amber (the other two parties being the compute provider and the software) brings new objectivity, independence, and increased assurances to users.
Today we’re excited to announce that Project Amber is taking an important step forward with a new proof of concept by the health group of Leidos, a $13.7-billion, 44,000-person, global leader in the integration and application of information technology, engineering, and science to solve customers' most demanding challenges.
"With the introduction of Project Amber at Intel Vision in May’22, Intel is taking confidential computing to the next level in our commitment to a zero-trust approach to attestation and the verification of computing assets at the network, edge and in the cloud,” said Greg Lavender, Intel senior vice president, chief technology officer, and general manager of Software and Advanced Technology Group (SATG). “I am excited to collaborate with Leidos to reflect the momentum that we are building with Project Amber and confidential computing.”
IoT Devices Complicate Data Security
Leidos’ Health Group is a provider of healthcare solutions to enable and improve the delivery of care, from life sciences to medical exams and the technology in between. The Health Group is building a proof of concept for the Project Amber attestation service for potential use in its QTC Mobile Medical Clinics, which uses large, specially equipped vans to perform “in-the-field” medical exams and health information processing for U.S. veterans in rural and underserved areas. The company is looking to Intel’s new offering and trusted hardware platform to play a key role in meeting complex new security challenges, many caused by connected devices on the Internet of Things (IoT) and Medical Internet of Things (MIoT).
Realize it or not, health care today relies heavily on medical professionals having cross-platform access to real-time data from wearables to medical devices for diagnosis. Unfortunately, the number of data-points contained on these devices exponentially increases the risk of exposing patient sensitive data. The solution: A renewed focus on moving beyond compliance and building resilient cyber physical systems.
Leidos’ Health Group works to protect multiple attack vectors including in-memory attacks. Leidos QTC is eager to deploy Project Amber Attestation and Intel® Software Guard Extensions (SGX) to create an independently verified hardware root of trust and trusted distributed compute foundation. These capabilities will help protect connected clinical workloads and data in storage, data in process, and data while being transmitted . Mitigating the risk of memory attacks is a huge step forward.
A cornerstone of Zero Trust
A big challenge is choosing between the plethora of products available to support zero-trust implementations. How do you get there from where you are today? What will give customers the biggest bang for their buck given the products that are already deployed? Can those products be configured or integrated to move forward toward a zero-trust architecture? To best respond, Leidos continually scans the market for emerging technologies to add to its large toolbox.
Increasingly, organizations in the federal market are considering managed services like Project Amber (as opposed to buying products outright). Leidos Health Group believes this business and deployment model provides more flexibility and speed for innovation. That in turn increases time to value, while reducing or even eliminating customer need for capital investment.
New flexibility
The Leidos proof of concept is still in its early stages. We both are optimistic that Project Amber will empower veterans and health care professionals to trust systems processing personal health data. Vendor-independent attestation will make it much easier to more securely move confidential computing workloads across environments, whether public and private cloud, edge, or on-premise.
In fact, Leidos already has expanded the concept of “on premise” beyond conventional hybrid cloud deployments. One of their digital twins mimics an upgraded Mobile Medical Clinic, with Gramine and Intel Xeon CPUs supporting Intel Software Guard Extension (SGX). The other digital twin employs the same technology, natively hosted within Microsoft Azure. Both use Project Amber’s attestation service.
And importantly, Project Amber frees Leidos from the need to build and maintain a complex and expensive attestation system. That lets the company focus on core differentiation like intelligent automation and AI/ML-driven analytics.
The Leidos mobile medical clinic proof of concept is a great use case example of Project Amber’s attestation service. Many are sure to follow. Stay tuned.
References: https://www.nextgov.com/media/leidos_tl01_cyber_214617_vf.pdf
Surveying the castle: New approaches to assessing Zero Trust Readiness Levels | Leidos
Smart Hospitals Powered by Intel and Intel's Ecosystem Partners
Advancing Confidential Computing with Intel’s Project Amber
Notices and Disclaimers:
Intel technologies may require enabled hardware, software or service activation.
No product or component can be absolutely secure.
Code names are used by Intel to identify products, technologies, or services that are in development and not publicly available. These are not "commercial" names and not intended to function as trademarks.
Your costs and results may vary.
© Intel Corporation. Intel, the Intel logo, and other Intel marks are trademarks of Intel Corporation or its subsidiaries. Other names and brands may be claimed as the property of others.
 Anil Rao is vice president in the Intel Office of the CTO and responsible for Security and Systems Architecture for Intel Corporation. Rao leads technical vision, strategy, and architecture for next-generation cloud to edge to client security, heterogeneous systems architecture including disaggregated and container computing, and Graph and Sparse AI.
Rao joined Intel in 2016 with two decades of engineering, product and strategy expertise in cloud and data center technologies. He was a co-founder of SeaMicro Inc. in 2007 developing energy-efficient converged solutions for cloud and data centers. After SeaMicro was acquired by Advanced Micro Devices (AMD) in 2012, Rao spent three years as corporate vice president of products in AMD’s Data Center Solutions Business Group. He served as technical adviser and strategy consultant to the office of the chief technology officer at Qualcomm until joining Intel.
Rao earned a bachelor’s degree in electrical and communications engineering from Bangalore University in India, a master’s degree in computer science from Arizona State University, and an MBA degree from the University of California, Berkeley. He is a co-author of the Optical Internetworking Forum’s OIF specifications and holds several patents in networking and data center technologies.
Anil Rao is vice president in the Intel Office of the CTO and responsible for Security and Systems Architecture for Intel Corporation. Rao leads technical vision, strategy, and architecture for next-generation cloud to edge to client security, heterogeneous systems architecture including disaggregated and container computing, and Graph and Sparse AI.
Rao joined Intel in 2016 with two decades of engineering, product and strategy expertise in cloud and data center technologies. He was a co-founder of SeaMicro Inc. in 2007 developing energy-efficient converged solutions for cloud and data centers. After SeaMicro was acquired by Advanced Micro Devices (AMD) in 2012, Rao spent three years as corporate vice president of products in AMD’s Data Center Solutions Business Group. He served as technical adviser and strategy consultant to the office of the chief technology officer at Qualcomm until joining Intel.
Rao earned a bachelor’s degree in electrical and communications engineering from Bangalore University in India, a master’s degree in computer science from Arizona State University, and an MBA degree from the University of California, Berkeley. He is a co-author of the Optical Internetworking Forum’s OIF specifications and holds several patents in networking and data center technologies.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.