0
0
2,195
As part of Intel’s ongoing commitment to security, we collaborate closely with and support academic research into the prevention, detection, and mitigation of potential security threats. We do so through programs such as the Intel Bug Bounty Program, our vulnerability disclosure program, and Intel Labs academic and faculty research grants and partnerships. On March 10, 2021, we announced the newest addition to this program portfolio: The Intel Hardware Security Academic Award.
The award is aimed at fostering innovative research into solutions, tools, and methodologies to address fundamental security challenges and enhance the industry’s ability to deliver more secure and trustworthy foundational technologies. Security researchers were invited to submit recently published papers which demonstrated outstanding novel research with a meaningful impact to the hardware security ecosystem.
This week Intel announced the winners of the inaugural Hardware Security Academic Award at the 2021 IEEE Symposium on Security & Privacy, a leading academic conference. The winners produced outstanding, impactful research which considered fundamental security challenges with long term relevance to academia, industry, end users. The awards were presented by Isaura Gaeta, Vice President of Security Research at Intel.
About the Winners:
This research proposes a new mitigation strategy for transient execution attacks at the microarchitecture level that integrates the best of prior mitigation strategies - it offers a principled approach toward more secure and performant speculation. A key novelty of SDO is that its way to approach the problem is to add more predictors, which seem to be counterintuitive since transient execution attacks were due to hardware predictors. SDO's observation is that by ensuring the prediction and resolution are independent of speculative secrets, it's safe to predict how a transmit instruction is executed.
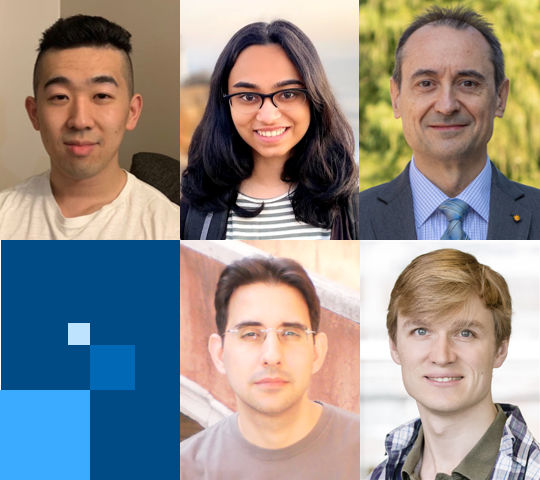
The winning team is comprised of:
This research presents a methodology to translate security critical properties crafted for a particular hardware design to another design, both within as well as across architectures. The first work of its kind, Transys attempts to shape product security assurance more towards science than art. It seeks to improve security assurance efficiency and scale by leveraging prior investments. High quality properties from a design can be reused, enriched, and extended to another design, reducing potential errors and misses through the convention labor- and expertise-intensive process.
The winning team is comprised of:

An video overview of this outstanding research is available HERE
Honorable Mention:
“CaSA: End-to-End Security Analysis of Randomly Mapped Caches” Thomas Bourgeat (MIT), Jules Drean (MIT), Yuheng Yang (MIT/University of Chinese Academy of Sciences), Lillian Tsai (MIT), Joel Emer (NVIDIA/MIT), Mengjia Yan (MIT)
“Constant-Time Foundations for the New Spectre Era” Sunjay Cauligi (UC San Diego), Craig Disselkoen (UC San Diego), Klaus V. Gleissenthall (UC San Diego), Dean Tullsen (UC San Diego), Deian Stefan (UC San Diego), Tamara Rezk (INRIA), Gilles Barthe (MPI-SP, Germany/IMDEA)
About the Process:
A committee at Intel examined the viability, novelty, originality, and relevance of all submissions with a focus on demonstrating significant contributions to the state-of-the-art and long-term relevance to the hardware security industry. The committee selected first and second prize winning teams out of 26 papers, featuring more than 80 authors across 14 countries. An award of $75,000 and $50,000 (first and second prize, respectively) will be granted to the winners’ academic institution to be used for further research or curriculum development support (such as class material, conferences sponsorship, computer lab infrastructure, web site development, textbooks and more).
What’s next? We look forward to continuing our close collaboration with the ecosystem. For researchers who are interested in submitting a paper for next year’s program, more information will be available here in the coming months!
About Intel
Intel (Nasdaq: INTC) is an industry leader, creating world-changing technology that enables global progress and enriches lives. Inspired by Moore’s Law, we continuously work to advance the design and manufacturing of semiconductors to help address our customers’ greatest challenges. By embedding intelligence in the cloud, network, edge and every kind of computing device, we unleash the potential of data to transform business and society for the better. To learn more about Intel’s innovations, go to newsroom.intel.com and intel.com.
© Intel Corporation. Intel, the Intel logo and other Intel marks are trademarks of Intel Corporation or its subsidiaries. Other names and brands may be claimed as the property of others. No product or component can be absolutely secure.
The award is aimed at fostering innovative research into solutions, tools, and methodologies to address fundamental security challenges and enhance the industry’s ability to deliver more secure and trustworthy foundational technologies. Security researchers were invited to submit recently published papers which demonstrated outstanding novel research with a meaningful impact to the hardware security ecosystem.
This week Intel announced the winners of the inaugural Hardware Security Academic Award at the 2021 IEEE Symposium on Security & Privacy, a leading academic conference. The winners produced outstanding, impactful research which considered fundamental security challenges with long term relevance to academia, industry, end users. The awards were presented by Isaura Gaeta, Vice President of Security Research at Intel.
About the Winners:
First place, $75,000: “Speculative Data-Oblivious Execution – Mobilizing Safe Prediction for Safe and Efficient Speculative Execution”
This research proposes a new mitigation strategy for transient execution attacks at the microarchitecture level that integrates the best of prior mitigation strategies - it offers a principled approach toward more secure and performant speculation. A key novelty of SDO is that its way to approach the problem is to add more predictors, which seem to be counterintuitive since transient execution attacks were due to hardware predictors. SDO's observation is that by ensuring the prediction and resolution are independent of speculative secrets, it's safe to predict how a transmit instruction is executed.
The winning team is comprised of:
- Jiyong Yu, University of Illinois at Urbana-Champaign
- Namrata Mantri, University of Illinois at Urbana-Champaign
- Adam Morrison, Assistant Professor, Blavatnik School of Computer Science, Tel Aviv University
- Josep Torrellas, Saburo Muroga Professor of Computer Science at the University of Illinois at Urbana-Champaign
- Christopher W. Fletcher, Assistant Professor, University of Illinois at Urbana-Champaign
Second-place, $50,000: “Transys – Leveraging Common Security Properties Across HW Designs”
This research presents a methodology to translate security critical properties crafted for a particular hardware design to another design, both within as well as across architectures. The first work of its kind, Transys attempts to shape product security assurance more towards science than art. It seeks to improve security assurance efficiency and scale by leveraging prior investments. High quality properties from a design can be reused, enriched, and extended to another design, reducing potential errors and misses through the convention labor- and expertise-intensive process.
The winning team is comprised of:
- Rui Zhang, University of North Carolina at Chapel Hill
- Cynthia Sturton, Associate Professor, University of North Carolina at Chapel Hill

An video overview of this outstanding research is available HERE
Honorable Mention:
“CaSA: End-to-End Security Analysis of Randomly Mapped Caches” Thomas Bourgeat (MIT), Jules Drean (MIT), Yuheng Yang (MIT/University of Chinese Academy of Sciences), Lillian Tsai (MIT), Joel Emer (NVIDIA/MIT), Mengjia Yan (MIT)
“Constant-Time Foundations for the New Spectre Era” Sunjay Cauligi (UC San Diego), Craig Disselkoen (UC San Diego), Klaus V. Gleissenthall (UC San Diego), Dean Tullsen (UC San Diego), Deian Stefan (UC San Diego), Tamara Rezk (INRIA), Gilles Barthe (MPI-SP, Germany/IMDEA)
About the Process:
A committee at Intel examined the viability, novelty, originality, and relevance of all submissions with a focus on demonstrating significant contributions to the state-of-the-art and long-term relevance to the hardware security industry. The committee selected first and second prize winning teams out of 26 papers, featuring more than 80 authors across 14 countries. An award of $75,000 and $50,000 (first and second prize, respectively) will be granted to the winners’ academic institution to be used for further research or curriculum development support (such as class material, conferences sponsorship, computer lab infrastructure, web site development, textbooks and more).
What’s next? We look forward to continuing our close collaboration with the ecosystem. For researchers who are interested in submitting a paper for next year’s program, more information will be available here in the coming months!
About Intel
Intel (Nasdaq: INTC) is an industry leader, creating world-changing technology that enables global progress and enriches lives. Inspired by Moore’s Law, we continuously work to advance the design and manufacturing of semiconductors to help address our customers’ greatest challenges. By embedding intelligence in the cloud, network, edge and every kind of computing device, we unleash the potential of data to transform business and society for the better. To learn more about Intel’s innovations, go to newsroom.intel.com and intel.com.
© Intel Corporation. Intel, the Intel logo and other Intel marks are trademarks of Intel Corporation or its subsidiaries. Other names and brands may be claimed as the property of others. No product or component can be absolutely secure.
About the Author
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.