- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have a design that relies on RSU for remote updates. I currently encrypt the .pof file for JTAG programming. When generating that encrypted .pof file, I also choose to generate the .rpd files that go into CFM1. When downloading the .rpd files with the encrypted .pof and .ekp programmed via JTAG, the RSU is unsuccessful. I see a revert to application image 0, which my design will only go to if there is a problem with application image 1. The encrypted .pof file does not seem to like downloading a n.rpd file.
Is there any way to get an .rpd file to download with an encrypted .pof
Link Copied
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
if referring to : https://www.intel.com/content/www/us/en/docs/programmable/683762/21-4/generating-the-initial-rsu-image.html
"For security application when you need to generate a signed or encrypted .rbf file, you need to first generate .rbf file from a .sof file, and only then generate the initial RSU image from the .rbf file."
Is it possible to follow above instruction for security application?
regards,
Farabi
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That document refers to a Stratix10, I am using a Max10. I can try the equivalent on Max10.
The process for generating the encrypted files is as follows:
1. Compile design, .sof is created
2. Take .sof into Convert Programming Files
3. Using .key file, generate encrypted .pof and encrypted .rpd and .ekp file from the base .sof
4. JTAG program the encrypted .pof with the .ekp
What you're telling me to do is add a step in step 3 where I would generate a .rbf file from the .sof, then encrypt that .rbf to make an .rpd file that is encrypted that can be downloaded into flash?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This does not work. Please advice. Is there a way, on a MAX10, to perform a remote update with encryption enabled?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
Could you please provide any error message or screenshot when the issue occurred?
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is no option for "Internal Configuration" when trying to convert programming files with .rbf. The design uses MAX10 internal flash, not a QSPI.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
Sorry for the late reply. Could you please take a look at the following steps on Generating files for Remote System Upgrade on page 8:
Generating files for Remote System Upgrade
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the document. Currently I am able to successfully perform an RSU with an .rpd file without encryption.
As soon as I choose to use an encrypted .pof, the .rpd file generated in the same step (from checking the generate .rpd box) does not work. I do a readback of the boot source register in the dual boot IP and the device is booting from the fallback image. This only happens when using the encrypted option.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
I'm not sure you have taken a look the following steps on generating .ekp File and Encrypt Configuration File in the User Guide on page 41 as I'm assuming there could be some problems on the file generation.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
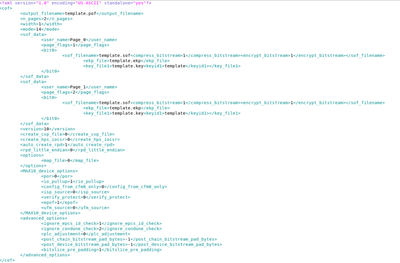
Hello, this is the .cof file I am using to generate the encrypted .pof and .rpd. I have a script that replaces the generic values with the inputs to the script that are the respective .sof, . ekp and .key file. The generated .pof is labeled as "encrypted" and the CFM 1 .rpd file is used and the other 2 are removed because I do not use those. This .cof is identical to how the unencrypted one works except for the .key/.ekp fields which are excluded. The same process is used to give me the final .rpd and .pof but the unencrypted version works perfectly and the encrypted one does not.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
My apologies for the late reply. I am checking this internally for more clarification
Will get to you once there are any findings.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
Sorry for the delay in response. From your flow, nothing sounds out of the ordinary to me.
- May I know if this is a singular case or are you seeing the same issue in other new devices?
- Can you consistently replicate this issue?
- Can you try to perform a full chip erase and see if the issue still persists?
Please let me know if this works for you. Thank you.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
1. This issue follows other boards, although they are all the same board design.
2. Yes this issue will always happen. Downloading the .rpd will work and boot into the application image every time without encryption but will not work when trying with encryption.
3. Full chip erase does not help the issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
Sorry for the delay in response. I couldn't replicate your issue on my end. What version of Quartus you're using and cand you try to use the latest version?
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
Just want to check whether you have tried the 3.8.3.2. Integrate the .ekp into .pof Programming (Page 55) when programming the FPGA with Initial Image using JTAG using the Programmer window?
Also, please check the Configuration Image Outcome Based on Encryption Settings (Page 56) from the same document as the Encryption Settings may affect the result for this process.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am using Quartus 21.1 but I can try the latest version.
Yes, I have been using 3.8.3.2 o on the document you linked to do all the programming so far. I tried 3.8.3.1 but my device would not boot.
I select the encrypted .pof image, right click and add the .ekp file generated in the same step, and also select an .ips file. I am not sure if the .ips file affects this but the .pof programming will fail without using an .ips file. This is done with an EtherBlaster. I can try a USB blaster but that should not make a difference.
If I am reading that table right, both images are encrypted with key x, and key x is loaded while programming. Config_sel pin is set to 1 so the device should boot into image 1, which it does without encryption
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
We are consulting engineering on this request. I'm planning to get back to you once I receive the update.
Sorry for the inconvenience caused.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
My apologies. I'm still waiting for a response from the internal expert.
Let me follow up again with them and will get back to you.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
I tried to do some research on this issue. I found a record that previously there was an issue with MAX 10 having a failure on performing RSU with encrypted POF. The engineering was able to come up with a workaround by using JTAG to program encrypted .jic to QSPI instead. You may refer to the guideline under 1.7.2. Programming the QSPI sub-topic in the AN 741: Remote System Upgrade for MAX 10 FPGA Devices over UART with the Nios II Processor user guide. I'm afraid this is the only possible workaround provided by the engineering team since MAX 10 is quite an old device. Hope it works.
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rt52,
I wish to follow up with you about this case.
Do you still have further inquiries on this issue?
Else I would like to have your permission to close this forum ticket
Regards,
Fakhrul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for looking into this. Unfortunately this design does not have a QSPI chip and only uses the internal flash of the MAX10, is it possible to use the .jic format to program to the internal flash?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page